Following is a guideline on setting up PowerShell remoting in an azure VM so that another azure VM in same Virtual Network, is able to execute PowerShell commands on the remoting enabled virtual machine. This will allow to setup as a test farm to run with visual studio team service or with TFS (will be discussed in a future post).
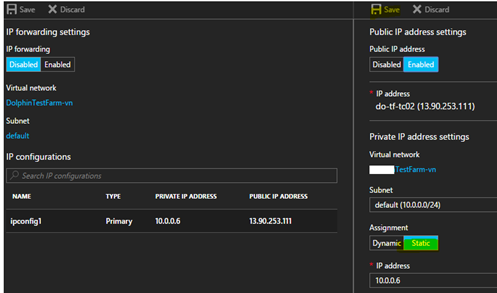
1. Assign internal static IP address for the virtual machine(s). You can do this by going to Virtual Machine setting in Azure Portal.
Then select the network interface, IP Configurations
Set the assignment to static. This will make the internal IP unchanged, when the machine is restarted.
Doing it with PowerShell explained here.
2. Execute the command to enable PowerShell remoting in the virtual machine. (run PS as administrator)
Enable-PSRemoting
This will throw an error which is bit of misleading and not providing enough information. If your virtual machine is not in a domain this might occur. More details discussed in below link.
https://4sysops.com/archives/enable-powershell-remoting-on-a-standalone-workgroup-computer/
This can be fixed by running the command with –SkipNetworkProfileCheck switch.
Enable-PSRemoting –SkipNetworkProfileCheck
3. From another virtual machine in the same virtual network in azure, you should be able to enter into a remote PowerShell session, and execute commands in the remote machine. But again this fails with another error.
Enter-PSSession –ComputerName <remotemachinenameorip> –Credential <remotemachineadminuser>
Enter-PSSession -ComputerName do-tf-tc02 -Credential do-tf-tc02\doadmin
Connecting to remote server do-tf-tc02 failed with the following error message : The WinRM client cannot process the request. If the authentication scheme is different from Kerberos, or if the client computer is not joined to a domain, then HTTPS transport must be used or the destination machine must be added to the TrustedHosts configuration setting. Use winrm.cmd to configure TrustedHosts. Note that computers in the TrustedHosts list might not be authenticated. You can get more information about that by running the following command: winrm help config. For more information, see the about_Remote_Troubleshooting Help
4. To fix this issue, add remote machine name to trusted hosts in the client of remote PS.
Set-Item -Path WSMan:\localhost\Client\TrustedHosts –Value <remotemachinenameorip>
Set-Item -Path WSMan:\localhost\Client\TrustedHosts -Value do-tf-tc02
With this PS session can be obtained.
5. Test the PS remoting. Create directory to verify the session is working.



![image_thumb[4][1] image_thumb[4][1]](https://blogger.googleusercontent.com/img/b/R29vZ2xl/AVvXsEg_6dcS_d4YCIi-ion6yUPcQfFCbVthr4kSQvhAk06-bd55wySiTWWvJTzs_3eDb9lk632RsxO8yvMVf3f3gdUjFhQbv1zaLGQ0MggEtAg-wOqrNddAqWz8E4MEsaxFfFBXICjgXabLxUpe/?imgmax=800)
![image_thumb[5][1] image_thumb[5][1]](https://blogger.googleusercontent.com/img/b/R29vZ2xl/AVvXsEj_8owZw8CkUOglSY9Hqz25GpRy_eW2zlEJjCuZQZTa1wJENpD_fqJQhGqlMIDNHqkJ65hWvSjl0_vGkXJUaE1zH6lLNck6oFsjgCWYEjki0J1FlW7QnJppiP6RB_WTVJvlS7NQyXKK_YSj/?imgmax=800)
![image_thumb[9][5] image_thumb[9][5]](https://blogger.googleusercontent.com/img/b/R29vZ2xl/AVvXsEi55v0QbbhnSyxK9aYaQ6wZQptVR_rHa73Y_PhRUYonREDFjPqvX_Y4Sn0d5tWOzMkr-0Z0YeTkCW8tOJn1jVAFf9XEwDHWkEU82Jo-i6fICgCX5iPbaf_GJsZXHMieye7aSj4dTrlPpkI2/?imgmax=800)
![image_thumb[11][1] image_thumb[11][1]](https://blogger.googleusercontent.com/img/b/R29vZ2xl/AVvXsEhvjNtNva2uMIeXFM92AV508t98hUtvQXRBnBF0_Jz3kS2FoL-tNp9FuHxZG0wBWK5Bh75hwGA-9vx2pN1dzvn729Hm-ir8DknQ_wxcVTkHypbhD_RrL7KamIiNSIQQORRzq3bySQIMBI16/?imgmax=800)
![image_thumb[13][1] image_thumb[13][1]](https://blogger.googleusercontent.com/img/b/R29vZ2xl/AVvXsEhigD3n2mBWASjmrBkfjo0mq66RtI6DmMkLSxrhPE72s2J7crktpj-BfeQAdlSOFLdeIVnqhqn_DK8dsN_-pJFr8Akq36_fRWyl37klOVBeoAo1U3ibpNAlCiCh91mojcosE3wcXw_VJFsw/?imgmax=800)
![image_thumb[19] image_thumb[19]](https://blogger.googleusercontent.com/img/b/R29vZ2xl/AVvXsEjIiJvkCPt-__Ak6ZfS4uBjQ95J6AKP27UWGSBLgEhzKBXXpca3w9vUyyTMWXxbaALij-Z0RFR6ZvyKoQWwoEFwNS8osebEHQH0bvPWj7muqdU_HZTl1vuga4ObLBo591i0RCRrKzEBMwRP/?imgmax=800)





1 comment:
I get a lot of great information from this blog.Azure Online Training
Post a Comment